Read about an attack in which antivirus is turned into malware.
Windows 10: DoubleAgent zero-day hijacks Microsoft tool to turn antivirus into malware
Our summary of this article:
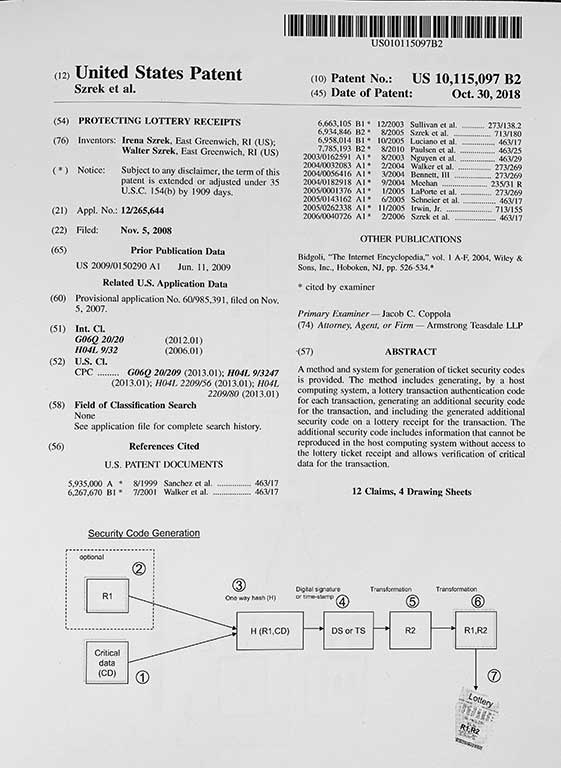
Turning antivirus into malware is an attack in which a person with access to the machine takes advantage of the vulnerability of the software to take control over the system or the applications installed on the system. This kind of attack, if well designed, is very difficult to detect and protect against. Even when access to the machine is limited because it is not on any network (i.e. an offline system), insiders can gain access to the machine. Any of the insiders – which in the case of lotteries would include the RNG vendor, draw personnel, the certification party, system administrators, operations personnel, and maintenance personnel – would simply need to install the fraudulent software on the machine.
To do this, an intruder can execute a different software or change the internal state of the machine, as in the famous attack by Eddie Tipton. And, as seen in this case, not only is it difficult to detect this kind of attack, it is also very hard to assess the extent of this kind of fraud.
Some lessons from this article:
- Each draw needs to provide nonrepudiation – proof of the origin and integrity of each draw. Nonrepudiation should be verified on an independent system. One cannot rely on a potentially defrauded system to prove its integrity.
At Szrek, we believe nonrepudiation of the generation process is key to RNG integrity. Nonrepudiation allows for independently verifiable proof of integrity of the random outcomes. Without nonrepudiation for every draw, lotteries can operate for years without knowing that their systems were defrauded. Our system allows for proof of integrity to be easily and quickly established for all past draws, even those made years ago.